Hello again, I’m Carl, I’m a player in the “Killing Floor 2” game, a “Controlled Difficulty” mod player, a KF2 modder, and a KF2 server hoster. This is the third and the last installment of the biggest drama of all times in the KF2 community history. It’s a great noir style detective & crime story, but it’s not fiction, it happened for real in this gaming community and I thoroughly enjoyed investigating it. It could very well be that it’s not over just yet.

Here I’m going to provide a detailed description of a particular Denial-of-Service (DoS) attack that was used to take down a number of popular KF2 servers and is active up to this day. The appropriate vulnerability is NOT patched and remains exploitable. I will identify Tamari and Forrest Mark X (FMX for short) as the primary suspects behind these attacks. This means that I do not have a direct and undeniable proof of proper attribution, because the attribution of these attacks is hard. Yet, this is normal in this industry and, given the general acceptance of this not perfect bar of evidence quality, it’s typically enough in this branch of information security to attribute DoS attacks to some particular actor. If you haven’t read it yet, please read the 1st part which covers the code theft situation here, and the 2nd part which covers the bans, the atmosphere of censorship on Tamari’s servers, as well as Tamari’s own type of personality here. These attacks successfully stifled, at the very least, the CD games from consistently going on my servers and did hurt a lot the gameplay on my HoE+ servers. These attacks also likely stifled the games on fanta’s HoE+ server. No matter what you think about all that and no matter if you find it convincing enough to attribute to Tamari and Forrest Mark X, it’s worth sharing this story to facilitate further information exchange, which, in the end, may help with establishing all that happened with higher level of certainty to it.
A quick rundown of the cyberattacks against competitors longread
- A number of popular KF2 HoE+ and CD servers suffered from DoS attacks throughout 2021 and 2022, specifically, fanta’s “HoE+” and Carl’s “Huwhyte oldschool HoE+ and CD” servers;
- Coincidentally, the owners of these servers are the people from whom Tamari and FMX stole the mods or otherwise consider them enemies;
- Coincidentally, these servers compete with Tamari’s servers in the same field, which are the servers that provide “Harder than HoE” game experience;
- Coincidentally, these DoS attacks either started or intensified at a point when the conflict was escalated;
- It is likely that either together or one of them on their own, Tamari and Forrest Mark X, are the perpetrators of these attacks;
- Tripwire Interactive refuses to fix the vulnerability described in this post;
- Tripwire Interactive removes any links to this web site from their official platforms, because exposing a cybercriminal, according to them, is “witch hunting” and “naming and shaming”, which isn’t allowed anymore. They amended all their official discussion platform rules to prohibit these things, so they can censor this information and ban participants who bring it up.
The nature of this Denial-of-Service attack
In general, Denial-of-Service attacks aim to make the service unavailable. In the case of KF2 server hosters, we provide a service to our users. Although we may not charge any fees to play our servers directly, some of us collect donations and definitely all of us incur hosting costs, so a case can be made that there was money loss due to the paid service not being available.
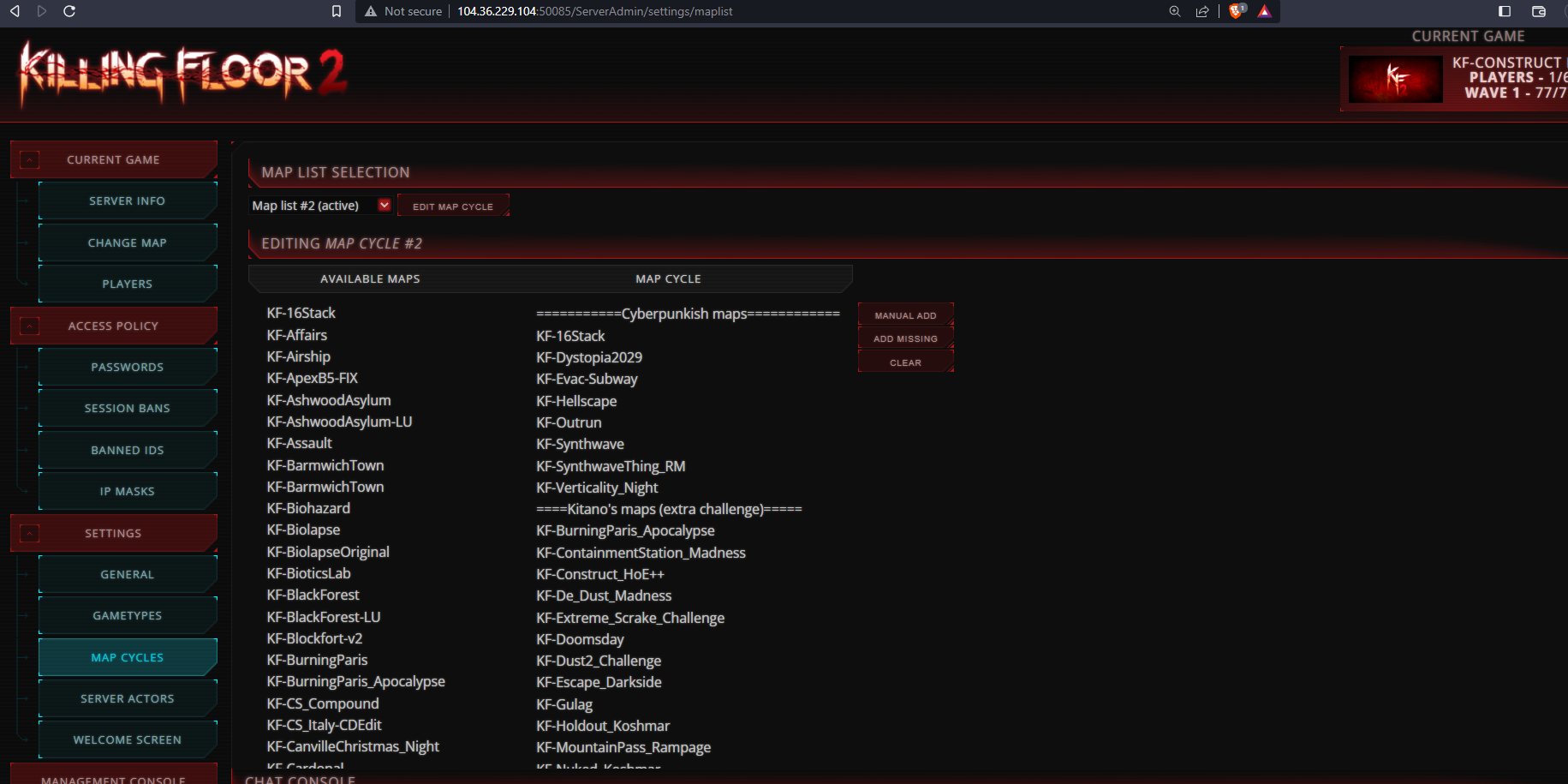
KF2 is built on top of Unreal Engine 3 (UE3 for short) and inherits most of its generic features. One of them is providing the administrative web console, which is, basically, a simplistic web server that can be configured to manage the games on the server. Running these web servers is not necessary to run the games on KF2 servers. However, it’s very useful to the point where pretty much every major KF2 hoster runs the administrative web servers, including TWI themselves. Here’s how it looks like opened in a web browser:
This web server is vulnerable to a buffer overflow attack. This is a type of attack which aims to provide a user input value longer than a certain variable can fit. This results in the “out-of-bounds” reference to memory, which, in general, leads to unpredictable program behavior, but in the case of UE3 web consoles it just reliably crashes them, taking with them the whole server. After a crash, depending on the way you set it up, the server either goes offline because its process has crashed, or it gets restarted by the systemctl or whatever means you chose to run as a daemon/service. A server crash/restart in any case means that any match that has been going on that server is ruined.
This vulnerability is as easy to exploit as to craft a specific URL and, say, put a wget or curl command into a scheduler that would call it periodically to crash any number of remote servers at the same time. One can go as high as invoking this scheduled task, say, once a minute. This can definitely completely deny any games on the attacked server, even if it’s configured to restart automatically. One can go as far as get the admin web console addresses for all the KF2 servers in the world and crash them all at the same time. If one engaged in it, it would completely deny all online KF2 gameplay.
The default address for the admin web console is the server IP address and the web console port 8080. To navigate there, assuming that the server IP is, say, 194.87.0.50, one would want to put this URL into their web browser: http://194.87.0.50:8080. Only a small minority of hosters go out of their way to change the default ports, but even when they do, they rarely go too far and their consoles can be discovered at adjacent ports, such as 8081, etc.
Moreover, shodan.io search engine can be used to get info on the web consoles already discovered by this helpful engine, even on unorthodox ports.
Most likely this thing applies to all and every UE3-based game, of which there are hundreds.
A very similar, if not this same vulnerability was previously reported by the almighty game security researcher Luigi Auriemma.
Don’t confuse the DDoS and DoS
Unfortunately, there’s a parallel thing that has been going with KF2 since at least 2021, which is distributed denial-of-service (DDoS) attacks. They are completely different from what I am going to discuss here, but for the sake of completeness I’m going to describe them as well, so there’s less confusion, but feel free to skip this section if you aren’t interested in it.
These DDoS attacks don’t target KF2 servers at all. These attacks, to be precise, are called amplification reflection-based volumetric L3/L4 distributed denial-of-service attacks. They work through complete saturation of the bandwidth of the internet connection of the target of these attacks with the useless garbage traffic nobody needs. KF2 servers, which are a flavor of Unreal Engine 3 (UE3) servers, are used to amplify traffic, because the KF2 server responses are roughly 700 more voluminous than the requests to connect from KF2 client software, which is, basically, your local PC KF2 game. The bad guys here emulate the behavior of the KF2 game through their custom malicious software, spoof the source address of the IP datagrams by substituting their own IP address with the IP address of their targets, and spam with this garbage all UE3 servers in the world they can find. The servers respond with 700 times more traffic, but instead of sending it to the bad guys, they send all this useless traffic to the targets, because they are tricked to do it by the fact that the source IP address was spoofed. Amplifying it 700 times while at it.
It’s not much different from the regular snail mail spoofing. One can put a different address into a “from:” field on the envelope and send to some place one knows to be prone with responding with a lot of useless paper. Because this one place is going to use the “from:” field contents to send the mail back, which is spoofed, some unexpecting person or organization is going to receive a lot of unsolicited mail.
These DDoS attacks have a clear purpose which lies outside of the KF2 community and has nothing to do with it. Their motives are clear, it’s either taking down the competitors in their business or holding the attacked companies or individuals for ransom, threatening with never stopping the attacks if the ransom isn’t paid. The majority of their targets are businesses, mostly various cloud services, including Google, Microsoft, OVH and other cloud providers. One of their biggest targets is Roblox, which is some kind of cloud service for building/running simplistic games. KF2 servers here just suffer from collateral damage that stems from abusing the fact that they 1) aren’t in position to verify the authenticity of the source IP address of the incoming datagrams 2) respond with 700 more voluminous responses and therefore are good for traffic amplification. More reading on the UE3 DDoS and general reading on amplification reflection-based volumetric DDoS.
Our case is completely different. The attack I’m going to describe in this post is a denial-of-service attack against the UE3 web server that exploits the out-of-bounds memory use vulnerability in said web server to reliably crash the server. These attacks are rare and very targeted. Their motive is always to take down the attacked KF2 servers.
The attacks against fanta’s servers
In the 2nd half of 2021 fanta’s servers were attacked with this DoS. At the time, as far as I remember, he was hosting 1 CD server named “Gulag CD” and 2 HoE+ servers, a regular one, very similar to the one he hosts these days, and another one which changed names periodically, but at one time it was called “HoE++| GREEN”. The duration of these attacks isn’t very well known and the fact that they have taken place wasn’t widely advertised, except for some hints in DMs. It took fanta some time to learn about this and find out the root cause of the server crashes.
It was around that time that the rumors of code theft by Tamari and Forrest Mark X started being circulated in fanta’s group, that was about the first time I’ve heard about them, at least.
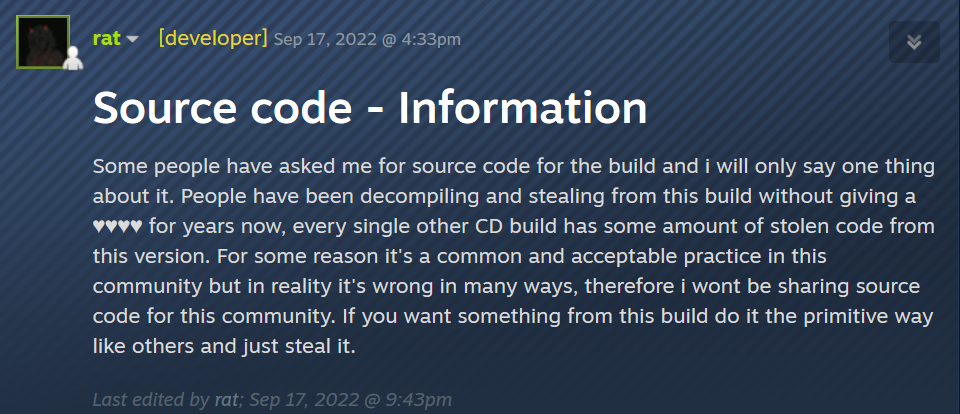
At the end of 2021 fanta added a variable name obfuscation to his “Controlled Difficulty Chokepoints Edition” to make it harder to decompile/reuse the code from CDCP:
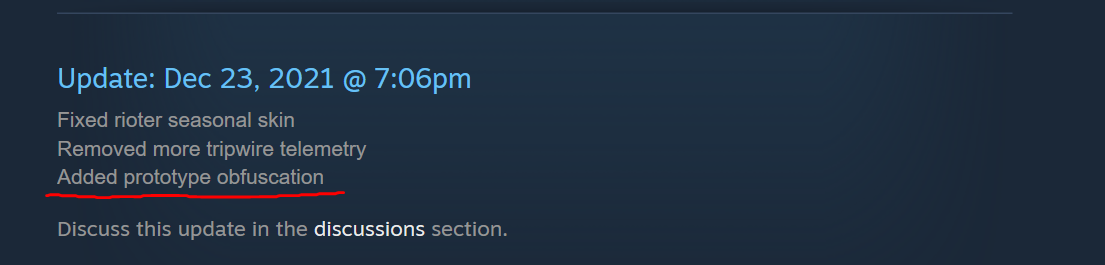
After said obfuscation was implemented, Forrest Mark X made this remark with someone on discord:
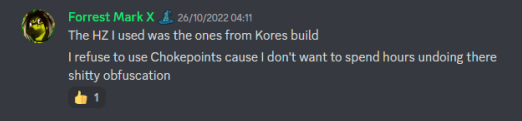
A number of things can be inferred from here:
- fanta knew that his mod was being ripped off and he introduced countermeasures to mitigate it;
- These measures aren’t bulletproof, but they make navigating and decompiling the mod’s code hard enough;
- These measures proved to be effective to a degree, according to Forrest Mark X himself, who found it harder to steal the CDCP mod’s code after the obfuscation was introduced;
- FMX admits that he does, indeed, decompile fanta’s CDCP mod, which is another piece of evidence proving him engaging in code theft, but since the obfuscation was introduced, it became hard for him to expand on it.
The attacks against Carl’s servers
It’s hard to establish precisely when the attacks have started, because of their rather sneaky nature. Any KF2 server periodically crashes on its own. Any KF2 server leaks memory if it’s left running for prolonged periods of time, e.g. weeks or up to a month. That’s why most KF2 server hosters reboot them periodically, some go as hard as reboot them once a day. Overall it’s not the most robust piece of software. Thus it’s natural to brush it off when it crashes as just “garbage software” and “it just happens”.
There are no meaningful events get written neither into KF2 logs, nor into system logs when a server is crashed remotely by exploiting this vulnerability. Yet, if you are a more or less experienced server hoster, you are in position to have a good feeling of how often does it crash on its own and in summer of 2022 I began suspecting that something abnormal may be going on, because of how suspiciously often it crashed, especially considering that it suspiciously crashed exactly when we tried to play the CD games.
But I had no idea where to look for and even at one point suggested that TWI themselves may be in the business of rebooting their KF2 servers remotely. In their Summer 2022 update they’ve introduced a sentinel runaway loop bug that was causing the KF2 servers to bloat and eventually crash and my thinking was they may had been trying to reboot the servers remotely that were stuck in the endless sentinel loop. Here’s a topic I’ve created on this on TWI forums:
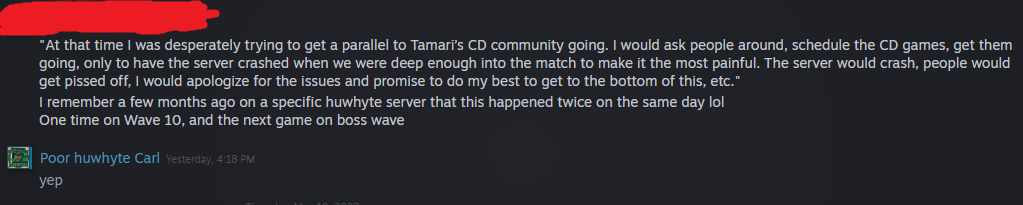
At that time I was desperately trying to get a parallel to Tamari’s CD community going. I would ask people around, schedule the CD games, get them going, only to have the server crashed when we were deep enough into the match to make it the most painful. The server would crash, people would get pissed off, I would apologize for the issues and promise to do my best to get to the bottom of this, etc. There were multiple witnesses to that who were present in these games that crashed, these are all well-known CD players, such as Lucid, Terry, Shogun Mod, Scum, Screwy Killer, St. Law, jings, etc. Some of them have retired since then.
My efforts in the end were futile and I have failed to get an alternative CD community going. A very significant factor that contributed to that were the constant server crashes. Nobody wants to schedule a game, play a few waves in order for the server to crash and all the progress wiped.
Other unknown attacks relying on the DoS against KF2/UE3 admin Web Consoles
It’s just to a very high degree a coincidence that we have someone who knows that this attack was used against two different independent KF2 server hosters. It’s very reasonable to expect that there were more of them, which I’m just not aware of. If you are such a server hoster and you suspect that your servers were attacked, I ask you to reach out to me to share your story. If your servers are being attacked right now — reach out immediately, so I can help with the defense and collect the forensic evidence.
DoS intensified
Fast forward to November 22nd, 2022. That was around the time when Forrest Mark X released his “Unofficial KF2 Patch”:
https://steamcommunity.com/sharedfiles/filedetails/?id=2875147606
I initially approved the release, the efforts and the functionality:
https://steamcommunity.com/groups/Huwhyte/announcements/detail/3470614896563573150
However, my opinion of it changed quickly after I realized that Forrest Mark X is at it again and violated other modders licenses by modifying and incorporating their mods into his “Unofficial KF2 Patch” mod, as well as obfuscated a good share of it. I’ve made an announcement about it in my Steam group discrediting the Forrest’s mod and Forrest himself :
But in Forrest’s case he straight up slaps in the face both Yoshiro and Molly (who serve as community engagement people at TWI) and states that his mod is whitelisted despite no authorization from TWI — well, if you do that and openly defy the authority of the game developer and therefore put yourself into a position where a developer can misconstrue your actions as “cheating” or “hacking” through the fact of defying their authority, all while publishing your mod in that game developer’s Steam content hub, you are past the point when said game developer might start thinking that you are doing something they don’t like. They don’t even have to understand what your code does — as you’ve stated that your code circumvents their policy yourself.
Thus, I officially revoke my endorsement of this patch, haha. Respect for the effort tho.
Because not sharing the source code and even more so obfuscating your mod is disrespectful towards the community. Fuck the UKF2P mod. Shame on you, Forrest. You’ve been naughty this Christmas season.
https://steamcommunity.com/groups/Huwhyte/announcements/detail/3505518337763746630
Coincidentally, the attacks against my servers had intensified that day and the intensity was such that basically denied all the gameplay. The attacks had intensified at 11:28PM CST. Initially, the attacks were performed most likely manually and were targeting my server #7, which caused the server to crash every other minute. By 11:45PM CST other my KF2 servers were included in the attack, causing them to crash every other minute. Needless to say, that this caused the players to be disconnected to much of their confusion. The timeframe was also very close to the primetime, which on my servers typically spans from 18:00PM to 3:00AM.
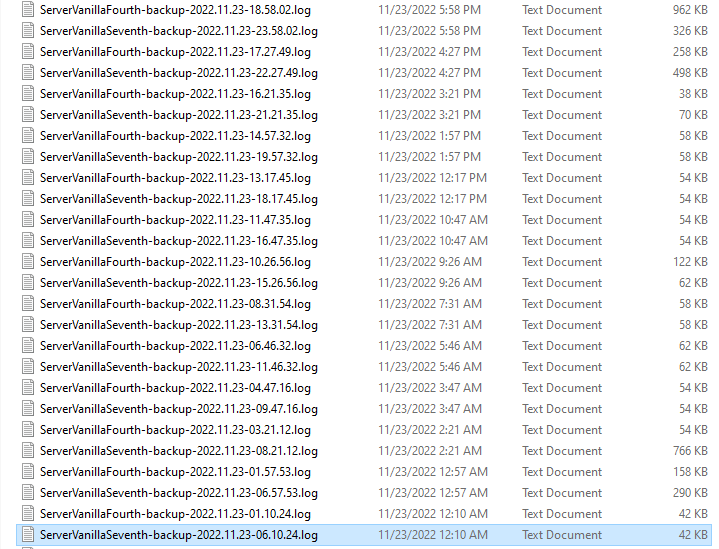
Around 12:10AM CST the crashes that had been happening almost every other minute in random fashion had stopped. My assumption is the attacker confirmed that no players are willing to join anymore and dispersed, which was satisfactory enough, and proceeded with setting up periodic attacks crashing the servers based on a schedule. The way KF2 works is the text log file which was current at the time the process has crashed gets archived (by adding “backup-YYYY.MM.DD-time” to its name) and a new log gets created, so the number of crashes per timeframe is easy to calculate by just counting the number of log files. Here’s how the appropriate KF2 server logs looked like in that period. Pay attention to the timestamps of the last change to each log file, which designates the last time when the log was written to. Also pay attention to the file sizes. Initially the file sizes were pretty big, which is naturally a result of KF2 servers running for a while, but then the file sizes are rather small, which hints that the KF2 servers which had written these logs didn’t have a chance to run for that long:
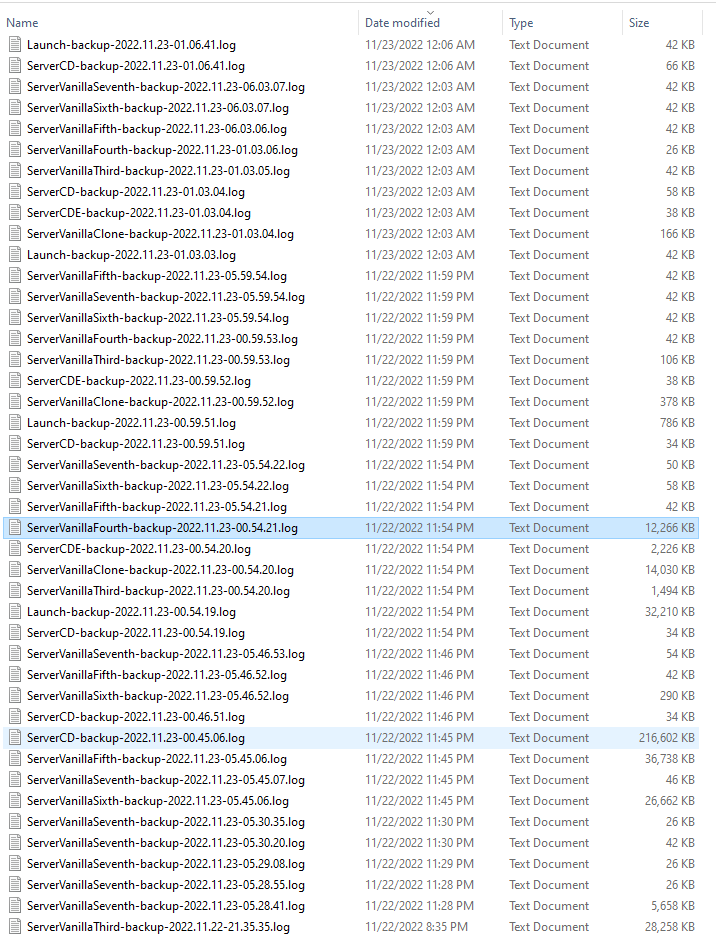
File sizes of about 26KB mean that the server just booted up and almost immediately was crashed again. File sizes a little above that, such as 42KB size, mean that since the server crash some players rejoined and probably had some games going on, but not for long.
After 12:10 AM 11/23/2023 CST a pattern emerged that indicated that servers #4 and server #7 were crashing once in about 1-1.5 hours per this schedule:
The other servers were attacked with much less intensity and could even had some successful matches in between the crashes.
Why servers #4 and #7 were targeted with more frequent attacks than the other servers? My guess is there are 2 reasons behind it. These are precision perk only servers that don’t allow any chaotic perks to be played, e.g. a firebug. I myself, as well as most of my online friends, play almost exclusively on these servers, to prevent unwanted interference from random joins choosing to play as chaotic perks. Another reason is Forrest Mark X enjoys playing a firebug perk and, in general, doesn’t like much the players who enjoy the purist precision only approach to this game and despises CD players in general.
Another peculiarity about servers #4 and #7 is they are hosted on 2 totally different VMs with cloud providers that have nothing in common. I do not use any configuration management software to manage these servers. Therefore, there’s absolutely no common factor between the two. And yet, they were crashing at the exact same time, which was a very strong indication that 1) it’s an external influence 2) most likely a malicious one.
That was the day when I completely threw away the stupid theory that my servers were crashing on their own, or the theory that TWI would reboot them remotely. That was the day when I realized what was the reason behind all these server crashes when I had been trying to get an alternative CD community going, had our matches crashing and had to apologize to everyone for these crashes.
You need to understand how pissed off I felt. Countless crashed CD matches. Countless apologies. Dozens of CD players pissed off because of these crashes. Pissed off at me, because they rightfully thought that it’s my servers that were the culprit here. And I was pissed at myself as well — how come other people had their servers going fine, while my crash all the time? I’ve spent countless hours sitting in gdb and analyzing those crash dumps. Staring at system logs for countless hours. Renting an alternative VM with different OS and different hardware, only to exclude the OS and hardware as a common factor. All futile, all the CD players giving up on me and my servers, because I can’t run them right and the CD games held on them crashing all the time.
And then, finally, I came to understanding that all that wasn’t just some random thing. Not the poorly written and poorly designed Epic UE3 engine software. Not some unreliable virtual hardware or operating system. No. It was SOMEONE WHO DID THIS TO ME. Willfully and consciously. Someone wanted my servers down. Someone, for months (at least!) pursued a conscious goal to stifle my efforts to build a parallel CD community in North America. And was successful at it. That’s not something that can be easily forgotten or forgiven. So I neither forget nor forgive.
Imagine getting banned by Tamari from playing the CD queues in NA, as for a few years his servers was the only place in NA when they were played. I said, okay, I’m going to mod the game myself, host my own servers and build an alternative community. Hundreds of hours invested and a few years later I got this all going to a degree. Nope, can’t have that. Someone keeps watching and wants to make sure that no such thing can exist.
After I realized that it’s definitely the external influence, which was probably the biggest and most important piece of information, the rest became routinely easy. I’ve done the network captures and quickly established the source and the nature of these attacks. Here’s how it looks like in wireshark:
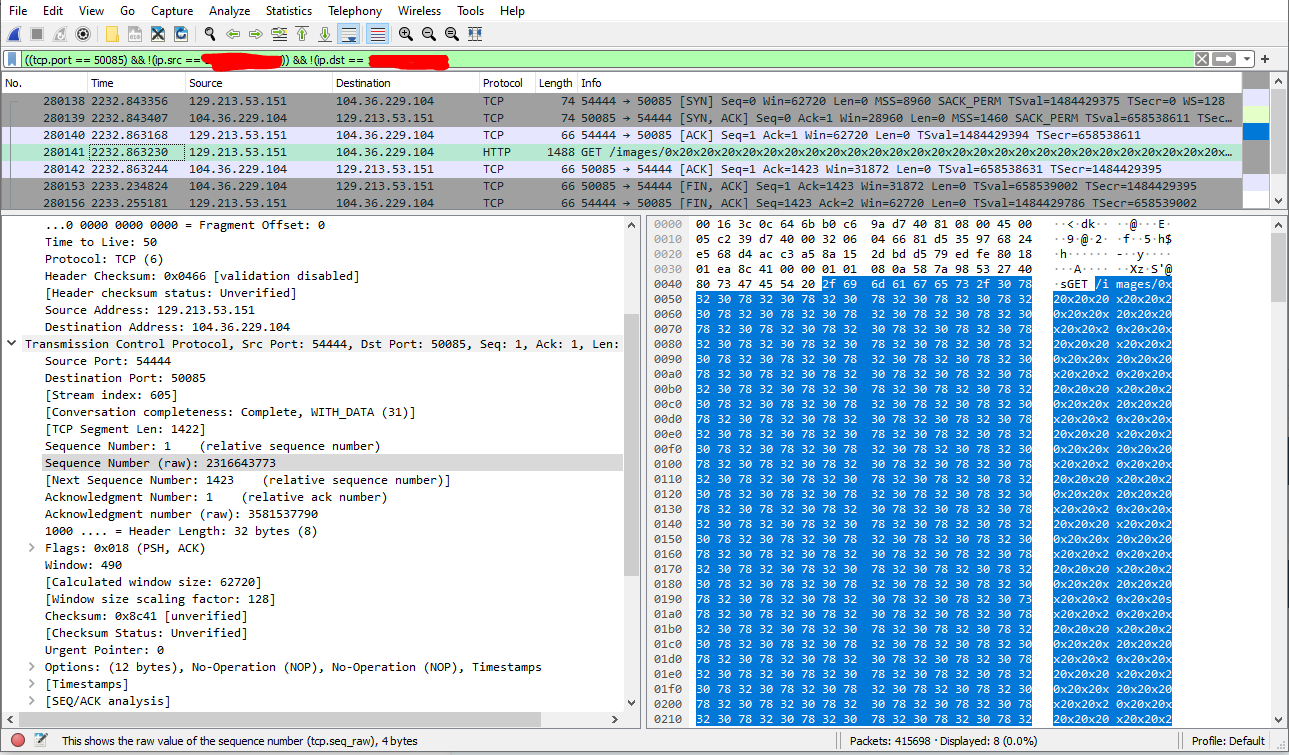
Things to note here:
- the screencap shows the real IP address of the attacker. It’s a rented free tier VM in the Oracle cloud;
- the content is just a very long string requesting a path after the /images/ via an HTTP GET request;
- the port on which the UE3 web server was hosted is non-standard, instead, it’s a higher number port 50085, that had to be necessarily discovered first through port scanning, which is typically considered as an aggravating factor of the cybercrime in the US court system.
The full GET request is this:
GET /images/0x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20sx20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20zdx20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x%C4%85E20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20xc20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x20x2 HTTP/1.1Host: 104.36.229.104:50085User-Agent: curl/7.68.0Accept: */*Note, that the string is pretty unique (try to search for it online).
Of course, Oracle isn’t sharing who rented this VM and what credit card was used to set up an account (supplying a valid credit card is required to set up an account with Oracle Cloud), at least without a subpoena. Still, it was another weird thing that hints that it was an amateur effort. The professional cybercriminals DO indeed use top cloud providers, including Oracle, but they do this with stolen credit cards, so it can never be traced back to their real world identities. Naturally, such rented VMs are necessarily short lived, because the stolen credit cards get blacklisted quickly, transactions get declined, the services get terminated. A much more prudent approach would have been if the malicious actors rented a VM from the 2nd or 3rd tier less known cloud providers who do not verify customers identities and accept privacy oriented crypto, such as XMR, as payments. But, for whatever reason, most likely just out of stupidity and not being able to think through the consequences, the actors rented an Oracle Cloud VM and used a valid credit card with it. Oracle is going to preserve this information for some time and it can be subpoenaed. I’ll let the bad actors keep guessing if I reported this case to the FBI Internet Crime Complaints Center and can theoretically get this information subpoenaed.
Such DoS attacks are definitely a federal crime in the United States under CFAA. It may result, upon conviction, in various fines and decades long prison time, depending on the damages inflicted and what the prosecution is able to prove. Still, even the time in federal prison of no more than 1 year, which is the minimum per CFAA, and some reasonable fine would be satisfactory enough punishment for this crime in my opinion.
Overall, this short-sighted amateur behavior suits both Tamari and FMX rather well. Think about it: who would steal other people’s mods in the first place, given that it’s almost inevitable that this code theft eventually gets called out? Keep in mind, that unlike this DoS issue, which leaves a small chance that it’s not them, the code theft situation by now is crystal clear — it’s 100% code theft situation and they 100% did this. A short-sighted amateur person whose planning horizon is very short to account for such long term consequences would do it. Any stolen code can be reused here and now, but what happens in a few years nobody knows, that’s a typical train of thought of such people.
Who would lie to cover up their traces? Again, any lie has an expiration date to it. Only truth stands forever. Eventually almost any conman gets caught and called out on their lies. Why would one lie? And understand this: they both lied extensively as thoroughly documented in part 2. Again, for short-term benefits stemming from the abuse of the initial trust of the people. Long term, however, people discover the truth and abandon the lies. Yes, it can take years, but it’s almost inevitable. The only type of people who just don’t get it are those with a very short planning horizon.
It also suits FMX a little better than Tamari. FMX always leaves an impression of being rather immature in the way he talks and acts. I’m not sharing any private chats or direct messages, but I hope that many of those who read this had a chance to chat with him more than once and know this first hand. Another hint showing this is how he treats his mods. Almost all of them are EXTREMELY bug-ridden, just check the comments section to his “Unofficial KF2 Patch” and assess the number of bug reports. I don’t envy the hosters who run it in the slightest, as their servers crash, some features straight up don’t work as advertised, etc. It’s his style of modding — make a change, release immediately, check if there are any complaints in the comments section, react to them “Oh, yeah, I forgot this one thing, addressed it now, here’s a new version”. Can’t he, instead, have some self reflection and inspect his code himself and test it thoroughly? No, he can’t for the most part. He may eventually learn and become less short-sighted, but for now it’s just the way he is.
Just to compare, almost none of it happens to, say, fanta. Or, say, Zedternal Reborn maintainers. Or myself. I’ve broken the games on my servers with a new mod release only once, in all these years, when I rolled out the “Homogeneous Fleshpounds” because of the hard to predict interactions that manifested themselves only in >1 player games.
DoS defense
I reached out to fanta who is on my friends list through some games we’ve played together and asked him if he knew anything about it. I didn’t think that he was behind this attack, but I had reasons to suspect that he might have been on the receiving end of these attacks in the past. He said he had been attacked in a similar way in the past. In a quick exercise we were able to reproduce the attack and thus confirm that the UE3 web server is indeed vulnerable and is trivial to exploit. We’ve also shared the indicators of compromise with each other, but more on this later.
Luckily, with this new intelligence from fanta and his help, I was able to quickly address the issue, so my servers were under this intense attack for less than a day, and I’m very thankful to fanta for that. If the malicious actors didn’t overplay their hand like that, they could’ve continued to keep sneakily ruining my and my friends games for months. But they did overplay their hand here. That’s another sign of immaturity and a lack or restraint.
It’s unlikely at this stage of the UE3 engine lifecycle that Epic fixes this issue. Therefore, my recommendation is to run a Web Application Firewall (WAF) in front of it and sanitize the length of the string a server can get after the /images/ path on the WAF. Many commercial WAFs are capable of that, as well as, I believe, mod_security can be used for that as well.
The simplest solution though, if one doesn’t want to bother with the complexities of the WAF, is to restrict the web server access only to a few necessary source IP addresses from which the server admins use it. Here’s an example of the allow rule for any Linux OS that relies on firewalld:
firewall-cmd --zone=public --permanent --add-rich-rule='rule family="ipv4" source address="1.2.3.4" port port="50080-50085" protocol="tcp" accept'I’m very thankful to fanta for providing the background for this attack and sharing his experiences and recollections, as this solidifies the case against Tamari & FMX as people behind these attacks.
DoS impact
Theoretically, before late 2022/early 2023, one could completely deny all the KF2 online gameplay by discovering all public KF2 servers via Steam API, discovering their web server consoles, and attacking them in a similar way my or fanta’s servers were attacked.
To prevent this from happening, I’ve reported this vulnerability to TWI and to the best of my knowledge they’ve reacted to it by putting a WAF that now protects their web consoles. I’ve never tried to verify that, it’s beyond what I typically do in my life and I am not a cybercriminal. Per responsible disclosure guidelines I had to abstain from sharing this information for a reasonable timeframe necessary for all vulnerable parties to meaningfully react to it and protect themselves. Yet, I was motivated enough to dig into Tamari’s & FMX KF2 server operation, which resulted in the first and the second part of this exposé being published. I’ve calculated that if they engage in the cyberattacks against their competitors, it’s very likely that they are just simply bad people and therefore a lot of dirt can be dug up on them if one just tries. Bad people always leave a trail of misdeeds and bad reputation behind them. It paid off, so the 1st and the 2nd part, that cover the code theft and BS bans on their servers now exist.

I’ve also contacted a couple of major hosters in this game (except Tamari, for 1 very important reason, but more on this later) and notified them about this vulnerability, e.g. Jordi (the guy behind the “maddubz” servers), BAz, Hunter, GenZmey (although he’s out of the game, but I hope he passed this on to his descendants) etc. I’ve also suggested publicly that the web server console should be firewalled, as it’s vulnerable to this DoS attack. If some KF2 server hoster keeps exposing their web server consoles unprotected to the outside world by now — it’s on them. There’s no centralized communication channel for KF2 server hosters they all listen on, so I’ve done what’s reasonably possible.
By now there still vulnerable KF2 servers do exist, especially from smaller and casual hosters, but one is no longer in position to completely shut down all online KF2, because all the aforementioned parties were warned about it and supposedly took various defensive actions they found appropriate.
It is, however, very sad and annoying that TWI have never communicated this issue to the server hosters, despite being informed about this vulnerability on November 28th, 2022. They have never made any public statement. They have never addressed the issue via a patch. If they aren’t in position to patch their server, because it is close to being abandonware at this point, they could have at least put a warning on their official wiki page describing the dedicated KF2 server setup, informing the hosters about the critical vulnerability and advising them not to expose the admin Web Consoles to the Internet due to them being vulnerable, or, at least, do it with a proper Web Application Firewall protection. As of now they are basically setting up new community KF2 server hosters for failure, by withholding this critical information. This is just plain unacceptable behavior in modern vulnerability and patch management in the software industry.
Moreover, not only they don’t communicate this critical information themselves, they deliberately censor references to this web site on their official TWI forums and maybe on other official platforms, and banned me for just making a reference to this web site in my profile signature. They have amended their forum discussion rules to include the clauses about the “naming and shaming” and “witch hunting”, likely introduced specifically to prohibit references to the information on this web site, because these newly added clauses were used in their bans/censorship justifications.
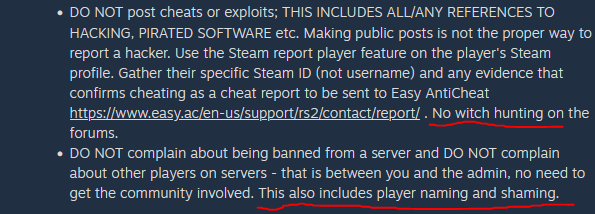
Note, that the TWI and their collaborators censorship, as well as the bans they have issued in violation of these novel rules and clauses are examples of the so called “ex post facto” punishment. This is a phenomenon in jurisprudence that describes situations when a law was passed to address some supposedly unwanted behavior and then applied retroactively to said behavior to punish the actor for violating the law that was passed after the actions took place. It is widely recognized as detrimental to justice and typically is discouraged. To the opposite, adherence to such practice is viewed as corruption.
The support ticket I have opened within TWI official support portal remained inactive for >1 year and finally was closed twice in May 2024, the first time because “the ticket was not receiving any updates” and for the second time without any meaningful explanation. TWI don’t do anything to address the situation themselves and hinder the community efforts, an enormous in its ridiculousness stance, one of the many such stances that emerge into a pattern.
The screenshots below show that TWI replaces references to www.zsdr.org on their official forums with asterisks and the concise ban justification they provided me with.

The actor behind the attacks against Carl and fanta is the same
There are very good reasons to believe that the actor behind these DoS attacks against fanta’s and Carl’s servers is the same person or a group of people.
Typically, in buffer overflow/out-of-bound memory access cyberattacks, a de facto standard is to use a long string of capital “A” for padding. The overflowing string would typically look like a long string of “AAAAAAAAAAAAAAAAAAA” that ends with the executable code, in the case of the “Remote Code Execution” exploits, but for simple crashing the code it’s not needed, thus, we don’t have it. Here we have a pretty unique string of “x20”, interestingly intermingled with “zd” and “%C4%85E”. These are most likely some remnants of some code. The “x20” most likely was previously a hexadecimal representation of the ASCII character known as “space”. The “%C4%85E” is some part of URL-encoded string with unclear meaning. The “zd” is too short to ring any bell, but might mean something. But all of them combined make a pretty unique signature string such, that if 2 independent parties were attacked with such a padding string, it makes it highly unlikely that these parties were attacked by independent actors. That’s one of the biggest reasons why hackers use “AAAAA” padding, so they look indistinguishable and cannot be tied through the use of unique strings to the same source.
I know for a fact that the padding string was exactly, 1:1 identical in fanta’s case. This is because I didn’t share with him the indicators of this attack, instead, I asked him to share his indicators first and he supplied me with the exact string that I’ve had. This leaves me with just 3 possibilities: it was a pure coincidence (extremely unlikely event, not much different from a monkey pressing the keyboard buttons randomly coming up with a meaningful phrase such as this one), or fanta is somehow tied to the attackers (unlikely, but more on that later) or we were attacked by the same actor (most likely). Because I trust myself to a high enough degree and actually you can trust me to a high enough degree to convey what I know truthfully and in full, because I’ve been around for a while, done and said plenty of things, and nobody caught me in any lies, this necessarily means that these 2 strings had to come from the same source for this situation to be reasonably probable.
This also hints that the attacker is not a mature professional cybercriminal. The attacker is likely to be an amateur, something I’m going to expand on later, as if they were a professional, they would use the “AAAAAAAA” padding.
Identifying Tamari and Forrest Mark X as primary suspects
In criminology and forensics there’s a notion of “motive, opportunity, means”, or “MOM” for short, that helps at narrowing down the circle of suspects from all the people who were never in position to commit a crime. Admittedly, identifying suspects is by far not enough to convict someone of a crime, but we aren’t in a criminal court either. We are in a court of public opinion. So it may worth documenting all these considerations. If new and more accurate information becomes known as a result of this exposé being published, it can help at establishing what’s wrong and what’s right with this analysis. The fact of the matter is the crime definitely has happened. And definitely the perpetrators of this crime do exist out there. The question is if they are Tamari and FMX or someone else? Here I’m going to carefully collect the arguments to establish whether it’s likely them or not.
Motive
Motive analysis is a staple of any criminal investigation. “Cui bono?“, or, “to whom it is a benefit” was a phrase commonly used by a Roman judge Lucius Cassius to emphasize the importance of the motive analysis in crime investigation. Just based on the motive analysis and lacking any other evidence it is common nowadays in cybercrime investigations to attribute the activity to specific actors. As an example, extensive DDoS attacks against newly added NATO member countries are commonly attributed to Russia in the media.
Obviously, we have a dedicated actor here. This actor has been engaging in these attacks for at least months against my servers and for years combined with fanta, until going into overdrive coincidentally on the day when I denounced the “Unofficial KF2 Patch” and Forrest Mark X himself. Therefore, we aren’t dealing with a casual. We are dealing with a person of a few games, so to speak. It’s a consistent player who plays this game for a long time and has enough concern about “Harder than HoE” experience and nuanced enough to know who hosts what and what “Harder than HoE” gameplay or what server owner they don’t like. You can easily cut off here all the casuals with not much time put into the game, say, roughly <1,000 hours.
Both Tamari and FMX are dedicated players, veterans of this game, Tamari has 7K+ hours and FMX has something like 3K+ hours. But, of course, we have probably hundreds of players who satisfy the >1K hours criterion.
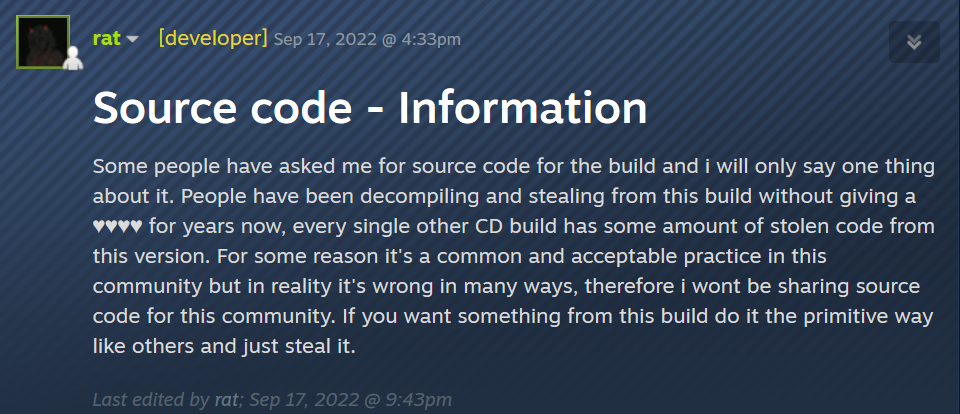
The actors behind these attacks have to hate specifically the way fanta and Carl designed their “Harder than HoE” gameplay on their servers or hate them personally for whatever reason. Well, fanta kept blaming FMX and Tamari for stealing his CDCP mod’s code. I quote:
Note here that fanta doesn’t name the names in this particular statement. I urged him to do it and eventually he did, but note here that he’s pretty reserved at what he claims, it’s typical of him, he tends to hold back on things he’s not 100% sure about, I’ll get back to this later. Carl kept retranslating fanta’s accusations:
So Carl and fanta at the time were the only 2 major server hosters, modders and CD players who were accusing Tamari and FMX of code theft.
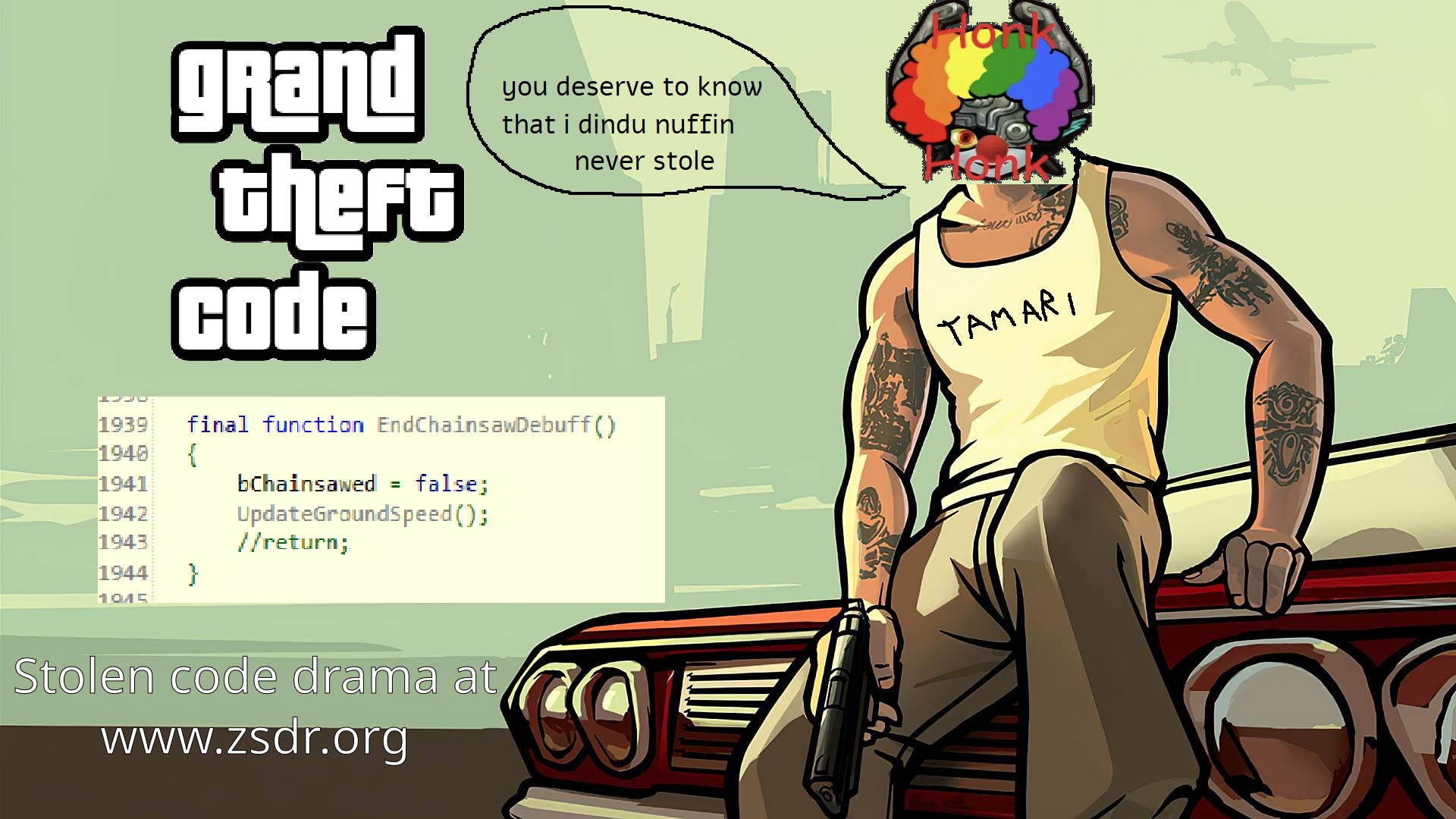
Note, that since then that definitive proof was found. There was someone (thank you!) who helpfully downloaded their ZEDModifications.u mod per my request which gave a start to the code similarity analysis which resulted in this proof being found. There’s much more than that, but at least this 1 single function was definitely stolen by Tamari and Forrest Mark X from the fanta’s CDCP mod:
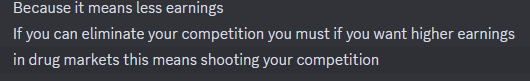
Moreover, to add insult to the injury, both fanta and Carl not only accuse Tamari and FMX of code theft, they host the respective “HoE+” and “HoE++” servers, no donations necessary. Both are significantly more popular than average and are full of players during prime time. But Tamari positions his servers as the best of this kind and collects donations from his frequenters. So it’s easy to see how the mere existence of Carl’s and fanta’s servers can get under his skin, both in terms of pride and profits.
Both fanta and Carl run CD servers as well. Moreover, Carl even dared to try and get a parallel to Tamari’s CD community running in North America. It’s easy to see how both Tamari and FMX would be happy if their competitors in the “Harder than HoE” space went down. And this was achieved to a degree, there’s no stable parallel CD community exists in North America as of now, and I pretty much all but abandoned my efforts to get one going, resorting to either playing HoE+ or occasional games with Europeans.
Taking down competitors isn’t anything new in the game server hosting. Moreover, one of the biggest, if not the biggest, botnets used for volumetric DDoS, the so-called “Mirai botnet”, was built by competing game hosters exactly for the purpose of taking down their competitors. A quote from the appropriate article by Brian Krebs:
Coelho told KrebsOnSecurity that the on-again, off-again attack DDoS method that Anna described using against Hypixel was designed not just to cost Hypixel money. The purpose of that attack method, he said, was to aggravate and annoy Hypixel’s customers so much that they might take their business to a competing Minecraft server.
“It’s not just about taking it down, it’s about making everyone who is playing on that server crazy mad,” Coelho explained. “If you launch the attack every 20 minutes for a short period of time, you basically give the players just enough time to get back on the server and involved in another game before they’re disconnected again.”
https://krebsonsecurity.com/2017/01/who-is-anna-senpai-the-mirai-worm-author/
That’s exactly what was happening here. The idea was to make the frequenters of my servers so pissed off at me, so they would blacklist my servers forever and switch to some other “Harder than HoE” servers. Such as Tamari’s. And this worked, to a degree, to impede the alternative CD community going by crashing the scheduled coordinated CD runs. It didn’t work as well for the HoE+ games, but just mostly due to their nature of people coming and going on a hop-on/hop-off basis, so people didn’t get as upset by sudden disconnects. And even with all that Tamari’s “Turbo Survival” servers were still less popular than my “HoE+”!
As one person who notices things wisely observed:
Also, consider that Tamari and FMX have been stealing other people’s mods for years without giving anything back. Only recently, FMX decided to get back to sharing his mods with the community, which is very commendable, but only after a years long hiatus when he was committing nothing to his github repo. It’s very easy to see, as I already expanded on this in the previous parts, that they didn’t want any competition to their servers, that explains not sharing back the mods with the community very well. Nobody in this world as of now can run the servers similar to Tamari’s. On the other hand, anyone can run servers with the CDCP mod. Anyone can run servers with almost all GenZmey mods. Anyone can run servers with CD Eternal Edition. Most of the appropriate mods are available in the Steam Content Hub Workshop.

My mods are an exception, but I’ve been declaring for years that I’m willing to share and I did share them in the past with hardcore players in S. America. It’s just I’m banned from the KF2 Steam Content Hub and can’t upload to the workshop, although it’s not a complete show stopper, it’s an annoyance enough to keep avoiding it. Hunter and fanta also don’t share their appropriate “Biohazard” and “HoE++” mods, most likely because they don’t want to bother with detaching them from the ranking system bypass methods, which typically result in the mods removed from the workshop and may result in a developer ban. Why Tamari and FMX don’t share their mods back? They do it so nobody else can run similar servers. So cyberattacks against the competitors is just a continuation of the same mindset — they not only want to avoid any competitors who can run similar servers, they attack the competitors who decide to run somewhat similar servers by building everything from scratch, from the ground up themselves.
So, to sum the motives up, here are the top 2:
- Revenge against the people who accuse Tamari and FMX of code theft and denounce them publicly;
- Taking down the servers competing in the same sector.

Opportunity
This paragraph isn’t of much interest, as traditionally for physical crimes this relies on the presence in the vicinity of the crime scene at the time of the crime. But on the internet everything and everyone is always connected. Yet, some educated guesses can be made and are actually common in attribution. For example, Kaspersky Labs have attributed Duqu malware to the Israeli state sponsored hackers because of the timezone activity and matching motives and means.
Here we have evidence supplied above of manual perpetrators activity around midnight time of the CST timezone. Which hints that the perpetrators are in the US of A. We also know that FMX is an adherent to a typical nerd “late at a PC” lifestyle through the times of his mods releases on the KF2 Steam Workshop. Although it’s less likely, it’s still probable that late Europeans or superlate/early Asians could have done it.
Another thing is the VM in the Oracle Cloud was US-based, rented from the East Coast Oracle Datacenter. Why US? Why not EU or Asia?
Means
Not everyone in the KF2 community is capable of pulling off these DoS attacks. Some technical penchant and knowledge of the game are prerequisites. The KF2 community is surprisingly narrow, both modders and hardcore players. But let’s just go through an exhaustive enumeration of everyone who is someone in this community.
- Tamari’s servers, with Tamari himself as a well known vet and a CD player and his friend Forrest Mark X as the modder behind all their mods (that aren’t stolen or ripped off property of other modders, of course, of which at least 5 were identified in part 1). It’s easy to see how FMX may know about quite a few vulnerabilities that exist in this game and how to exploit them. A subgroup of these people are those who on occasion play on Leg-End’s “Filthy Casuals” servers (he renamed his servers as of recent, probably didn’t like to be called out like that, no problem, I can always update and share his new server names, they just go by “CD #” these days), but it’s the same Tamari’s group, just to mention 1 thing: Leg-End himself has an “Admin” designation on Tamari’s servers (displayed with the help of the “YAS” mod, stolen from GenZmey, BTW). Almost everyone else is either a “Donator” on Tamari’s or otherwise affiliated. All that is US of A.
- Hunter and his group of players from Russia. Hunter is one of the 3 most knowledgeable people in this game overall, the other two being Forrest Mark X and fanta. He’s the author of the “Controlled Difficulty Eternal Edition” and the author of the “Biohazard” servers mods. He may also know quite a few sketchy things.
- fanta and his group of players. He’s the author of the Controlled Difficulty ChokePoints Edition, enough said. European Union.
- Carl, that is me. Another presumed Russian, allegedly residing in North America.
- GenZmey. Well-known and prolific modder from Russia whose mods are run by pretty much every modded server in this game. Including Tamari’s, in which case they are stolen, as they are abused in violation of GenZmey’s intellectual property rights, as stated in the licenses he used to protect his rights.
- Asapi, the author of the Controlled Difficulty Combined Edition and the hoster of a number of hardcore CD servers in Japan.
- If we are very picky we can also add the Chinese group of players (sino study CD, etc) and Thai group of players (Nekoha Club, etc). There are also a bunch of S. Koreans (e.g. “YellowGrapes”) who play most of the time either with the Japanese or with the Chinese or with the Thai people. We can also add some players from S. America, who oftentimes play on N. American servers and have some of their own servers going, but unfortunately they oftentimes go out of business, I’ve helped some of them with hosting in the past, but all these players have retired by now with a few exceptions. No notable modding detected.

That is pretty much it, folks. It’s that narrow. Notably, everyone from 1 to 5 run their own weird non-transferable mods most important parts of which aren’t shared with the public and not uploaded to the Steam Workshop and all of them somehow bypass the game ranking system.
That’s the full list. It’s highly unlikely that there’s an outsider not affiliated with any of these groups who would know the game well enough to know about this vulnerability and how to exploit it and be motivated enough to conduct these attacks for years on end. It’s very likely that the perpetrators are members of at least one of these groups.
But it’s worth noting that no other member of these groups has any beef with both fanta and myself, except for Tamari and FMX and might be some other people from their awkward quazi religious doomsday cult group.
Who was in the know?
Imagine you are a big figure in the KF2 community and host your KF2 severs and mod the game. Then, say, you decide that it’s time to sneakily DoS your competitors. What would be your first step?
The first question a potential attacker would ask is “Am I vulnerable to this as well?” They have to make sure that their own servers aren’t vulnerable against this, so they can’t be attacked back. Well, guess what, I’ve checked some of the servers hosted by the groups mentioned above in November 2022, and almost every one of them had their servers with fully exposed vulnerable web server admin console listening on the default port. With a few notable exceptions: 1) Tamari’s servers 2) fanta’s servers. This was the reason I didn’t bother contacting Tamari about this vulnerability, because, out of pure coincidence (wink-wink), his servers didn’t have a web server exposed to the whole world, at least on the well-known and/or default ports. Fanta’s servers are understandable, as he had to stop exposing the web server console to avoid the attacks he had endured in 2021.
This begs the question, why Tamari’s servers were exempt from exposing the web console? Everyone else was doing it. Hunter was doing it and is still doing it (this and the rest as of 5/16/2023). Jordi, the “maddubz” owner, was doing it and is still doing it. Moreover, when I asked Jordi about the incidence of sudden unexpected crashes he reported that he’s not aware of any, and he runs hundreds of servers, which just shows how rarely this vulnerability is exploited and how pointed and precise these attacks were. GenZmey was doing it. Although it can count as circumstantial evidence, it’s still evidence. It all adds up. Tamari, for whatever reason, but it’s likely that we know the reason, was NOT exposing his web consoles to the public internet. It’s as if he knew about this vulnerability and kept it to himself. And naturally made sure that his servers can’t be attacked with it.
Addressing less probable explanations
Theoretically, it can be argued that it was fanta who was behind these attacks. He has the means and the opportunity, but he lacks the motive. He had the unique padding string in that conversation that matched the padding string used in the DoS attacks against my servers, which can be construed as he is the source of it. There are, however, good arguments against it:
- fanta, overall, seems like a very reserved person who just would not say or do almost any stupid thing that can potentially bite him in the ass later down the road. It’s as if he plans his life carefully and naturally avoids any behavior that can potentially entrap him later. Such as lies or cyberattacks against competitors. Very unlike Tamari or FMX;
- fanta doesn’t seem to be a person who can be easily moved either way. Recall how I mentioned previously that initially he refused to name the names of the code thieves and limited himself to accusing just “some people” in code theft and “community” for tolerating it. And it took time and words for me to convince him to name the names. Moreover, in 2020 I’ve approached him to ask if he can share the way he mods this game on “HoE++”. He refused (understandable, as the potential for abuse is too high), however, he instead redirected me to check with Tamari, if he will be willing to share. If he was really moved by Tamari’s and FMX well documented scumbaggery as much, would he refer me to them? Similarly, I was referring any hardcore players who wish to play CD games in NA to Tamari’s, even long after he banned me from his servers, until I finally was fed up with their scumbaggery by the end of 2022;
- if it was fanta, what would be his gains from doing it? Why would he attack only my servers? For example, Hunter’s servers in Russia are much closer to his EU servers and through that Hunter is a much closer and impactful competitor. Yet, Hunter’s servers were never attacked, as Hunter doesn’t even care enough to stop exposing his web consoles to the Internet. Anyone in the know can take his servers down any moment, but nobody does. There’s no motive for fanta whatsoever to attack my servers;
- Then, if he did, why would he even respond to the private chat messages from me and immediately help me with addressing the situation? It would be much more natural for him to ignore me, exactly how FMX did behave, who denied my attempts to talk to him on the day when the DoS attacks against my servers had intensified.
Valley Center, CA
Among other things, fanta shared with me a residential IP address which he suspected was used as a source of these DoS attacks on at least 1 occasion. I hope it’s not a false positive. Sometimes the bad guys forget to use an Oracle Cloud VM as a proxy and attack directly. The residential IP can be geolocated to a small town in California, located roughly between Temecula and San Diego. Does anyone know if it’s where the Tamari’s residence was at the time when the attacks were happening? In any case, it’s a small detail that doesn’t add or remove much to the story.
The summary
To sum it up:
- Tamari and FMX have a well documented history of stealing mods and a well documented history of not liking being called out on that. Fanta and Carl were the only major KF2 figures who called them out on the mods theft at the time. Coincidentally, the servers of these two were attacked with this cyberattack by the same actor.
- Coincidentally, both Carl and fanta compete with Tamari’s servers in “harder than Hell on Earth difficulty” space. There’s a documented history of frustration Tamari had with the fact that his servers are less popular. It’s rather common in other games for the server hosters to engage in cyberattacks to topple their competitors.
- There are only roughly 7 groups of hardcore players in this game in the whole world. The rest just don’t care enough about all that, it’s very likely that only people from one of these groups cared enough to engage in cyberattacks and for years at that.
- The cyberattacks had significantly intensified coincidentally exactly on a day when a post in Carl’s blog was published which disparaged Forrest Mark X & Tamari and their mod.
- There are only 5 capable visible modders in this game who are in position to know the game well enough to know about this vulnerability and how to abuse it. It’s highly unlikely that an outsider did this.
- The organization of the attacks was rather sloppy, which suits the character of how Tamari & FMX do things, such as their mods development, or mods theft, or their community management rather well.
- It’s slightly likelier that the perpetrators of this crime reside in the Americas time zone than anywhere else.
- Coincidentally, only Tamari’s (and fanta’s, because he was attacked at that point already) servers weren’t exposing the vulnerable web console to the Internet, as if he knew about this. Everyone else either did expose it to the Internet or still does.
- Suspiciously, on the day when the attacks had intensified, Forrest Mark X refused to accept the friend request from Carl on Steam. Unlike fanta, who provided help, shared the evidence and coordinated the defense efforts which resulted in better understanding of what could be going on behind the scenes.
- Overall, Tamari and Forrest Mark X are the only people who match all the criteria in the motive, opportunity, means analysis.
Decide for yourself if all that is convincing enough.
Conclusion
In conclusion I’d like to bring this screencap once again:
At one point fanta marked his CD build as “archived” and hadn’t been playing this game for months. But in the recent months he resumed both maintaining the build and playing. I like to think it’s because, among other things, he found that not everyone in “this community” agrees that it’s an “acceptable practice” to tolerate the code theft.
Scumbags like Tamari and FMX go as far at their abuse as the community is willing to tolerate. And, unfortunately, I keep finding that yes, the KF2 CD player community is willing to tolerate that scumbaggery to a high enough degree. Keep in mind that what was described here and in the previous parts most likely is just a tip of the iceberg. I suspect that there were more questionable actions like that, but I’m not sharing just suspicions, at least just yet.
However, according to some members of this community, it’s people like me who are a problem. It’s me who wages a “segregation war” or “ignites the hatred”. Code theft is fine with these people. Don’t give a shit. BS bans are fine as well. Cyber attacks against the competitors — comes with the territory! But if you dare to call such a behavior out — you are a problem, you “ignite the hatred” and engage in “segregation wars”:
If this player weren’t that short sighted, he would realize that the CD he “just plays” exists because the appropriate modders wanted to create and advance this mod for this community. “For the bois” so to speak. It can be pulled from the Workshop any moment. TWI will surely break it with the next update. What are you going to be playing then, if you don’t give a shit? They can stop hosting any CD or HoE+ servers any moment, as they already did in the past. The mod authors aren’t happy when their mods are ripped off and you all don’t “give a shit” about it. It disincentivizes them from developing the mods further. Because that community finds nothing better, but to steal it and spit at those who merely question this behavior, the modders have less incentive to do anything for these people.
Can this player fathom that the mere KF2 CD mod that he plays on a weekly basis may stop existing soon, because he spits at the modders faces? If one wanted this mod to be advanced one would be prudent at respecting the mod and respecting the mod’s authors. Help the modders or at the very least not blame them when the modders defend their rights. But these people have not much respect for the mod or the modders, they are willing to “just play KF2” CD, but they treat the hundreds of hours spent developing these mods like nothing. THEY DON’T CARE. A mere questioning of the stolen code enablers, who are their supposed friends, weighs more for these CD players than any respect towards the mod.
There’s a reason why Hunter hasn’t fixed a simple issue with the “CD Eternal Edition” build since September 2020. There’s a reason Blackout had retired. There’s a reason fanta blames the community in his message. This reason doesn’t fully explain this behavior, but still is a significant factor. And this reason is why almost all current CD builds are fractured, abandoned, archived or even pulled from the Workshop completely. You, the community of KF2 CD players, did this. You don’t give a shit about “the stolen code fiesta”. You don’t give a shit about Tamari’s, FMX’s and their acolytes hypocrisy. You don’t give a shit about the cyberattacks. Yet you attack the modders and those who want to do the right thing on their behalf. Well, don’t act surprised when the modders and the server hosters don’t give a shit about you, through not investing time and efforts into developing CD, through ignoring the bugs and crashes, through pulling their content from the workshop altogether, like Kore or Tiger did.
Peak KF2 Drama *eats popcorn*
omg my crimes are being exposed wtf carl you mental psycho bigot right winger nazi i dindu nuffin
what the fuck are you talking about, you didn’t have enough bans?
lick my burgers, asshole.